MD5 is usually however Utilized in cybersecurity to verify and authenticate electronic signatures. Working with MD5, a consumer can verify that a downloaded file is reliable by matching the public and private key and hash values. Mainly because of the superior amount of MD5 collisions, on the other hand, this message-digest algorithm just isn't per
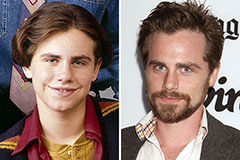 Rider Strong Then & Now!
Rider Strong Then & Now! Taran Noah Smith Then & Now!
Taran Noah Smith Then & Now! Michael Bower Then & Now!
Michael Bower Then & Now! Batista Then & Now!
Batista Then & Now! McKayla Maroney Then & Now!
McKayla Maroney Then & Now!